What is Blockchain Technology?
Complete guide • Cryptography • Applications • Examples
Blockchain Fundamentals:
Build Your BlockBlockchain is a distributed ledger technology that records transactions across multiple computers in a way that ensures security, transparency, and immutability. It uses cryptographic hashing to link blocks together, forming an unalterable chain of data.
Key blockchain concepts:
- Distributed Ledger: Records stored across multiple nodes
- Cryptographic Hashing: Unique fingerprints for each block
- Immutability: Once recorded, data cannot be altered
- Decentralization: No central authority controlling the system
- Transparency: All participants can verify transactions
Blockchain powers cryptocurrencies like Bitcoin and Ethereum, but also has applications in supply chain, healthcare, finance, and more.
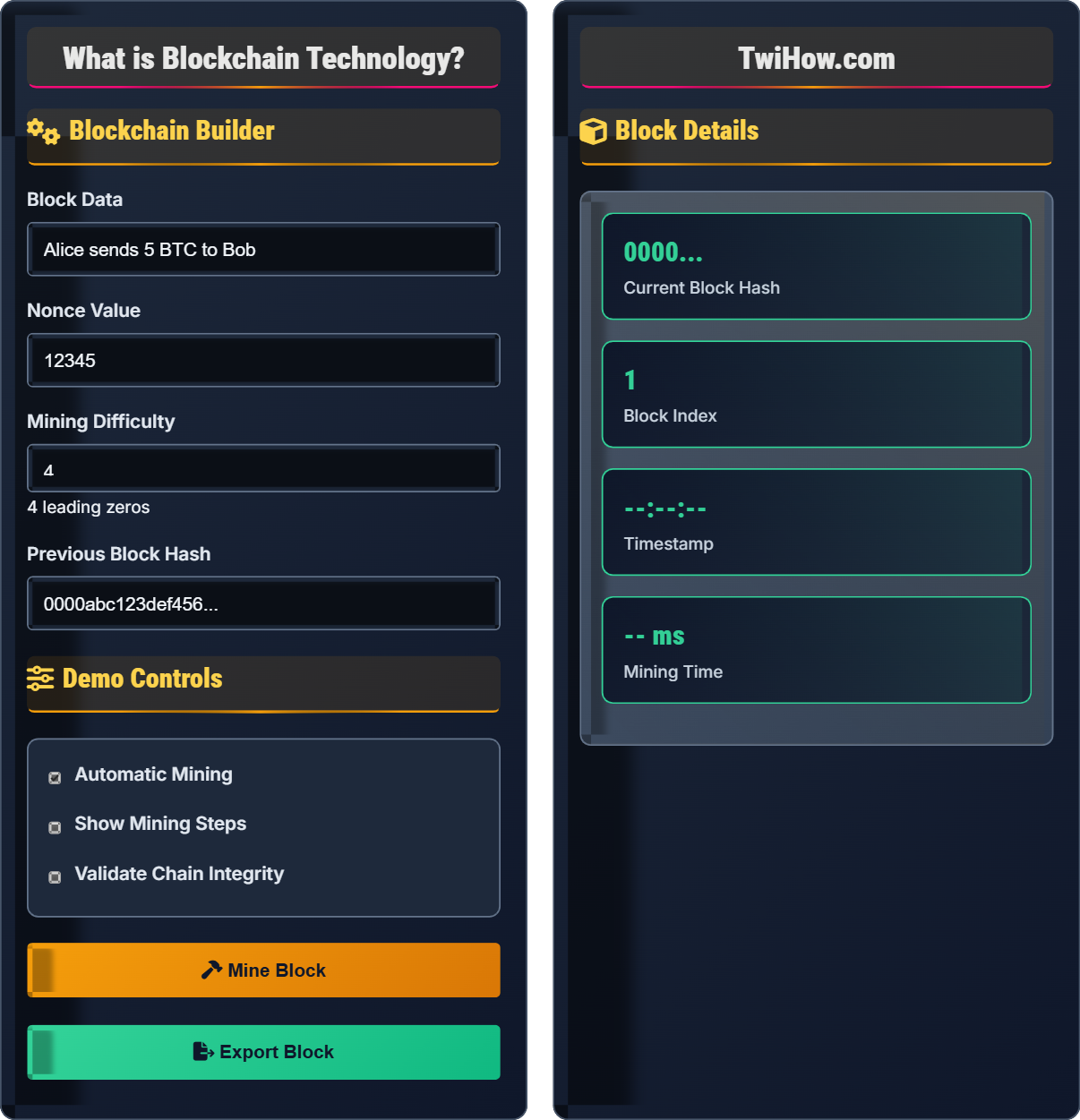
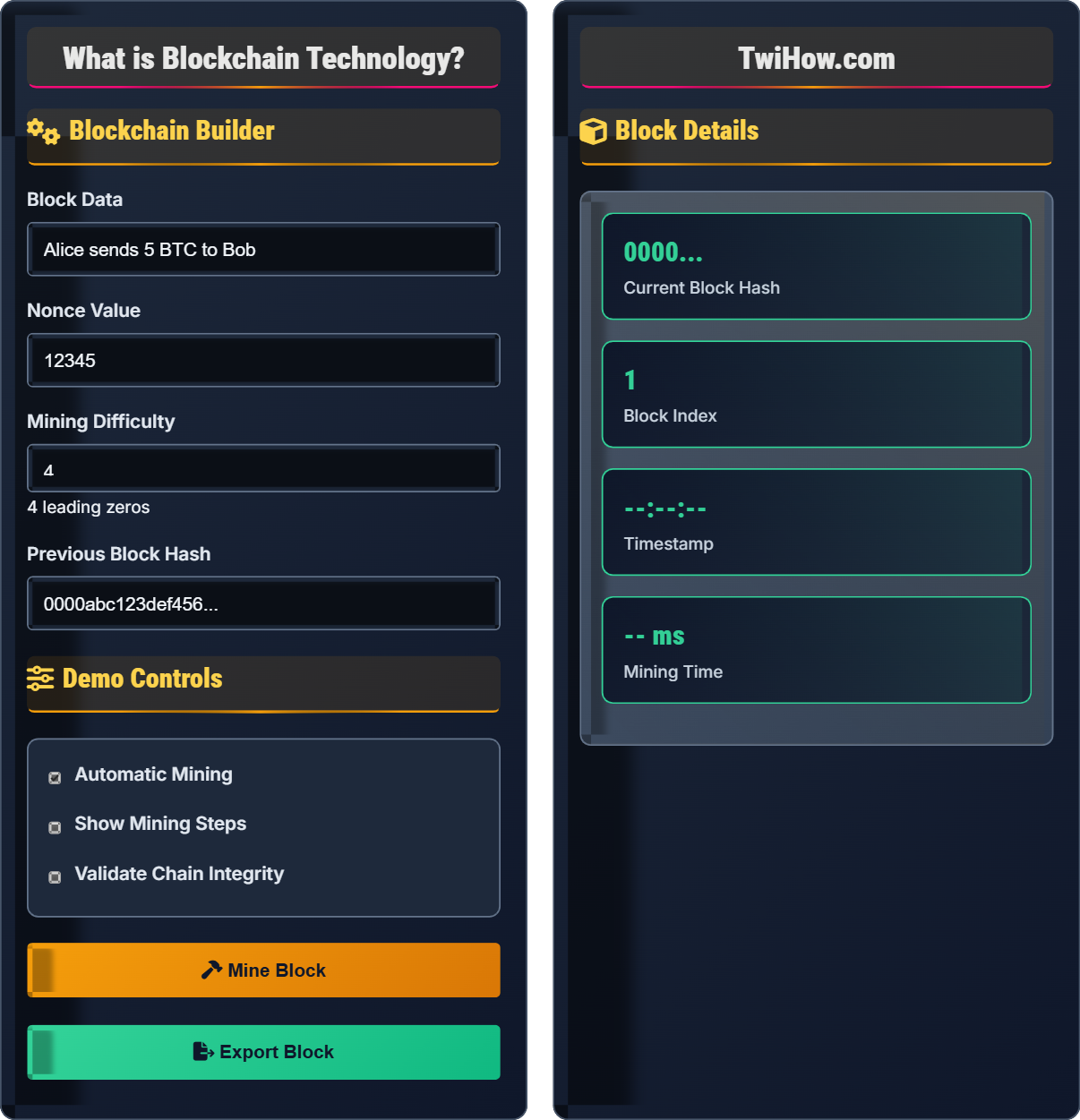
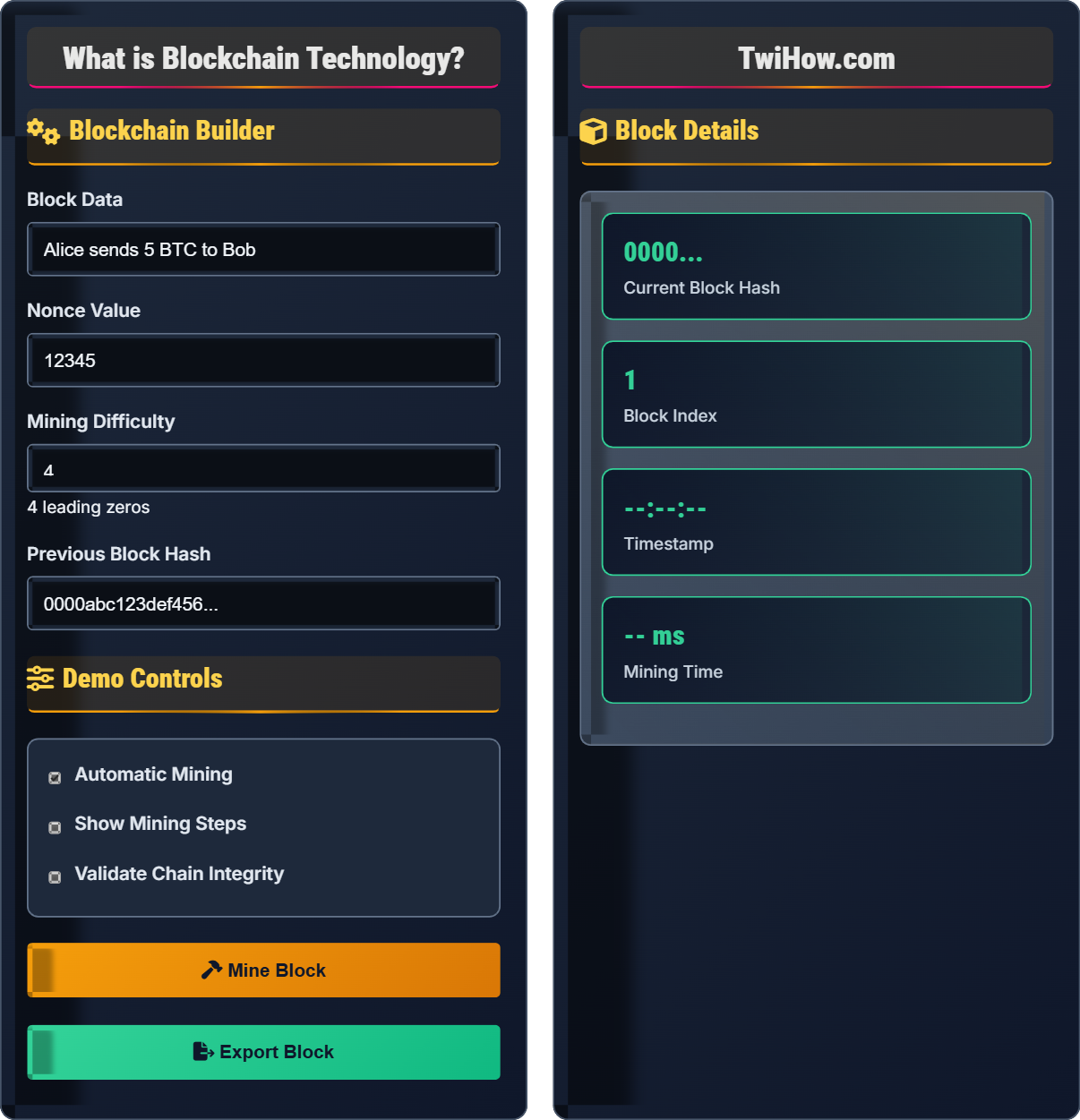
Blockchain Builder
Demo Controls
Block Details
Core Blockchain Concepts
A blockchain consists of a series of blocks, each containing a list of transactions. Each block has a cryptographic hash of the previous block, creating an immutable chain. This structure ensures that once data is recorded in a block, it cannot be altered without changing all subsequent blocks.
Block Components: Timestamp, transaction data, previous block hash, nonce, and current block hash.
Cryptographic hashing is a mathematical function that converts input data of any size into a fixed-size string of characters. In blockchain, SHA-256 is commonly used. The same input always produces the same hash, but even a tiny change in input creates a completely different hash.
Properties: Deterministic, fast to compute, infeasible to reverse, avalanche effect (small changes create large differences).
\( \text{Hash} = \text{SHA-256}(\text{Block Data} + \text{Previous Hash} + \text{Nonce}) \)
Consensus mechanisms ensure all participants agree on the blockchain's state. The most common are Proof of Work (PoW) and Proof of Stake (PoS). These mechanisms prevent double-spending and maintain network security.
Proof of Work: Miners solve complex mathematical puzzles to validate transactions.
Proof of Stake: Validators are chosen based on the amount of cryptocurrency they hold.
Miners compete to solve cryptographic puzzles using computational power. The first to solve the puzzle gets to add the next block and receives a reward.
Pros: Highly secure, battle-tested
Cons: Energy-intensive, slow transactions
Validators are chosen based on the number of coins they hold and are willing to "stake" as collateral. This is more energy-efficient than PoW.
Pros: Energy-efficient, faster transactions
Cons: Centralization concerns, complexity
Delegated Proof of Stake (DPoS), Proof of Authority (PoA), Byzantine Fault Tolerance (BFT), and others offer different trade-offs between security, speed, and decentralization.
DPoS: Delegates vote for validators
PoA: Identity-based validation
Blockchain Structure
Each block contains a hash of the previous block, creating an unbreakable chain. To alter a block, an attacker would need to recalculate all subsequent blocks, which is computationally infeasible. This creates immutability and trust without requiring a central authority.
Real-World Applications
Bitcoin, Ethereum, and other cryptocurrencies use blockchain to maintain a distributed ledger of transactions without a central bank or authority.
Examples: Bitcoin (digital gold), Ethereum (smart contracts), Ripple (cross-border payments)
Track products from origin to consumer, ensuring authenticity and quality. Walmart uses blockchain to trace food origins, improving safety and reducing waste.
Benefits: Transparency, authenticity verification, efficiency
Self-executing contracts with terms directly written into code. Execute automatically when predetermined conditions are met, reducing need for intermediaries.
Uses: Insurance, real estate, finance, legal agreements
Secure, verifiable digital identities that users control. Prevents identity theft and provides access to services without centralized databases.
Applications: Digital IDs, KYC processes, voting systems
Blockchain Knowledge Quiz
What makes blockchain "immutable" (unchangeable)?
Blockchain's immutability comes from cryptographic hashing and chaining. Each block contains a hash of the previous block, so changing any block would require recalculating all subsequent blocks, which is computationally infeasible. This creates a tamper-evident ledger.
The answer is B) Cryptographic hashing and chaining.
Immutability is the cornerstone of blockchain security. The cryptographic link between blocks means that altering one block requires altering all subsequent blocks, making tampering practically impossible. This property eliminates the need for trust in a central authority.
Immutability: Data that cannot be changed once recorded
Cryptographic Hash: Fixed-length identifier for data
Chaining: Linking blocks together cryptographically
• Hash changes with any data modification
• Requires changing all subsequent blocks
• Computationally infeasible to alter
• Think of it as a linked chain
• Breaking one link breaks the whole chain
• Each block is a "snapshot" of truth
• Confusing with database backups
• Thinking it prevents all attacks
• Not understanding the computational difficulty
Explain the difference between Proof of Work and Proof of Stake, and discuss the advantages and disadvantages of each.
Proof of Work (PoW): Miners compete to solve complex mathematical puzzles using computational power. The first to solve gets to add the next block and receive rewards.
Proof of Stake (PoS): Validators are chosen based on the number of coins they hold and are willing to "stake" as collateral.
PoW Advantages: Battle-tested, highly secure, resistant to certain attacks.
PoW Disadvantages: Extremely energy-intensive, slower transactions, centralization in mining pools.
PoS Advantages: Energy-efficient, faster transactions, more accessible participation.
PoS Disadvantages: Potential centralization among wealthy holders, complexity in implementation.
Consensus mechanisms solve the fundamental problem of achieving agreement in a decentralized system. PoW uses energy and computation as "skin in the game," while PoS uses economic stake. Both create disincentives for bad behavior, but with different trade-offs between security, efficiency, and decentralization.
Consensus: Agreement on blockchain state
Staking: Locking up cryptocurrency as collateral
Mining: Adding new blocks to the blockchain
• Security vs efficiency trade-off
• Decentralization is key
• Economic incentives align behavior
• PoW = computational work
• PoS = economic stake
• Consider sustainability
• Thinking PoS is less secure
• Ignoring trade-offs
• Not considering energy costs
An attacker wants to alter a transaction in block 5 of a blockchain that currently has 100 blocks. Explain what the attacker would need to do, why it's difficult, and what factors would affect the feasibility of this attack.
What the Attacker Must Do:
1. Recalculate the modified block 5 (including new transaction)
2. Recalculate blocks 6 through 100 using the new hash from block 5
3. Mine all 96 replacement blocks faster than the rest of the network
Why It's Difficult:
• Each block contains a hash of the previous block, so changing one requires changing all subsequent blocks
• Mining requires enormous computational power and energy
• The network would notice the longer valid chain and reject the shorter one
Factors Affecting Feasibility:
• Network hashrate (computational power)
• Number of confirmations (blocks after the target block)
• Economic cost of required hardware and electricity
• Time since the target block was added (more time = more security)
This example demonstrates the security model of blockchain. The attacker faces an exponential difficulty curve - changing one block requires changing all subsequent blocks. The deeper a transaction is buried in the chain, the more secure it becomes. This is why waiting for confirmations is important in cryptocurrency transactions.
Confirmation: Number of blocks added after a transaction
Hashrate: Total computational power of the network51% Attack: Controlling majority of network power
• Security increases with depth
• More computational power = more security
• Economic costs deter attacks
• Wait for more confirmations for larger amounts
• Older transactions are more secure
• Network size matters for security
• Underestimating computational requirements
• Not considering network hashrate
• Ignoring time factor
Design a simple smart contract for a crowdfunding campaign. The contract should accept contributions, keep track of the total raised, and release funds to the creator only if the target amount is reached within a specified time period. Otherwise, refund all contributors.
Smart Contract Logic:
1. Initialization: Set target amount, deadline, and recipient address
2. Accept Contributions: Allow deposits with time limit check
3. Track Progress: Maintain current total raised
4. Deadline Check: At deadline, check if target is met
5. Execute Outcome: If target met, send funds to creator; otherwise, return to contributors
Key Features:
• Automatic execution based on conditions
• Trustless operation (no intermediary needed)
• Transparent and auditable
• Irrevocable once deployed
Benefits: Eliminates need for trusted third party, ensures fair execution, reduces costs.
Smart contracts demonstrate blockchain's programmability. They automatically execute agreements when predetermined conditions are met, removing the need for intermediaries. This example shows how blockchain can replace traditional escrow services with a trustless, automated system.
Smart Contract: Self-executing contract on blockchain
Trustless: No need to trust a third party
Programmable Money: Currency with embedded logic
• Code is law in smart contracts
• Bugs are irreversible
• Logic must be thoroughly tested
• Start simple and test thoroughly
• Consider edge cases
• Use formal verification methods
• Not considering all edge cases
• Insufficient testing
• Ignoring gas costs
Which of the following is NOT a significant limitation of current blockchain technology?
Immutability and security are actually strengths of blockchain technology, not limitations. The other options are genuine challenges facing blockchain adoption: scalability issues limit transaction speeds, energy consumption is a major environmental concern, and complex interfaces hinder mainstream adoption.
The answer is C) Immutability and security.
It's important to distinguish between features and limitations of blockchain. While blockchain has genuine challenges like scalability and energy consumption, properties like immutability and security are core benefits that distinguish it from traditional databases. Understanding both strengths and weaknesses is crucial for appropriate use cases.
Scalability: Ability to handle growing transaction volume
Throughput: Transactions processed per second
Trade-offs: Balancing security, scalability, and decentralization
• Distinguish features from limitations
• Consider use case appropriateness
• Balance trade-offs
• Focus on actual problems
• Consider Layer 2 solutions
• Evaluate for specific needs
• Confusing benefits with limitations
• Not understanding trade-offs
• Applying to inappropriate use cases
FAQ
Q: Is blockchain just for cryptocurrencies like Bitcoin?
A: No! While Bitcoin popularized blockchain, the technology has many applications beyond cryptocurrency. Blockchain is being used for supply chain tracking, digital identity, healthcare records, voting systems, smart contracts, and more. Cryptocurrency is just one use case of the underlying distributed ledger technology.
Q: How secure is blockchain technology really?
A: Blockchain is extremely secure when properly implemented and sufficiently decentralized. The security comes from cryptographic hashing and the computational difficulty of altering the chain. However, security depends on factors like network size, consensus mechanism, and implementation quality. Individual wallets and exchanges can still be hacked, but the blockchain itself is very secure against tampering.