What is IoT?
Complete IoT technology guide • Step-by-step explanations
IoT Fundamentals:
Show IoT SimulatorThe Internet of Things (IoT) is a network of interconnected physical devices embedded with sensors, software, and connectivity that enables them to collect, exchange, and act on data. IoT transforms ordinary objects into smart, connected devices that can communicate with each other and centralized systems.
Key IoT components:
- Sensors: Collect environmental data (temperature, humidity, motion)
- Connectivity: Wi-Fi, Bluetooth, cellular, LoRaWAN communication
- Processing: Edge computing and cloud analytics
- Actuators: Physical components that respond to commands
IoT applications span smart homes, industrial automation, healthcare monitoring, agriculture, and smart cities, connecting billions of devices worldwide to create intelligent ecosystems.
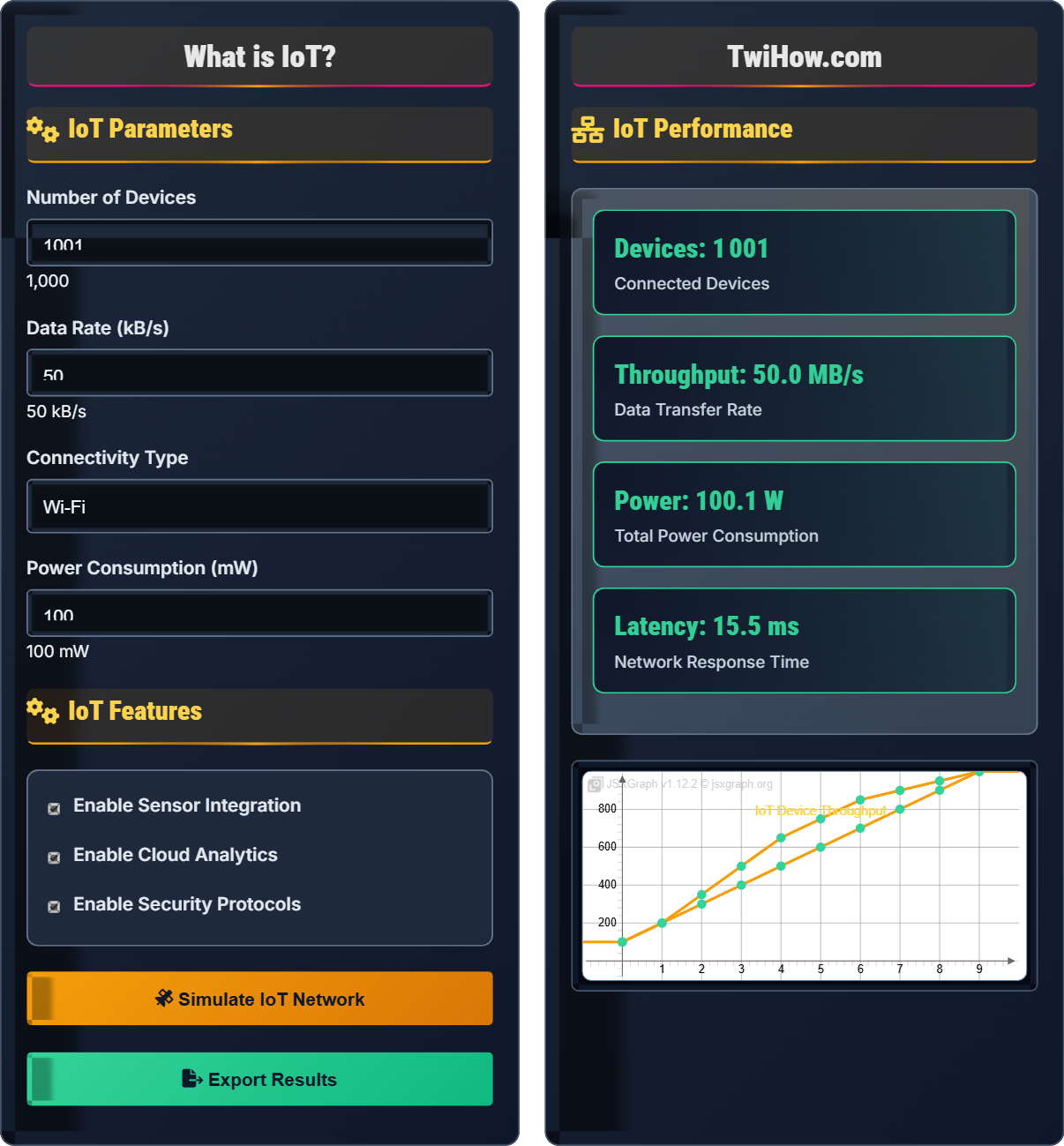
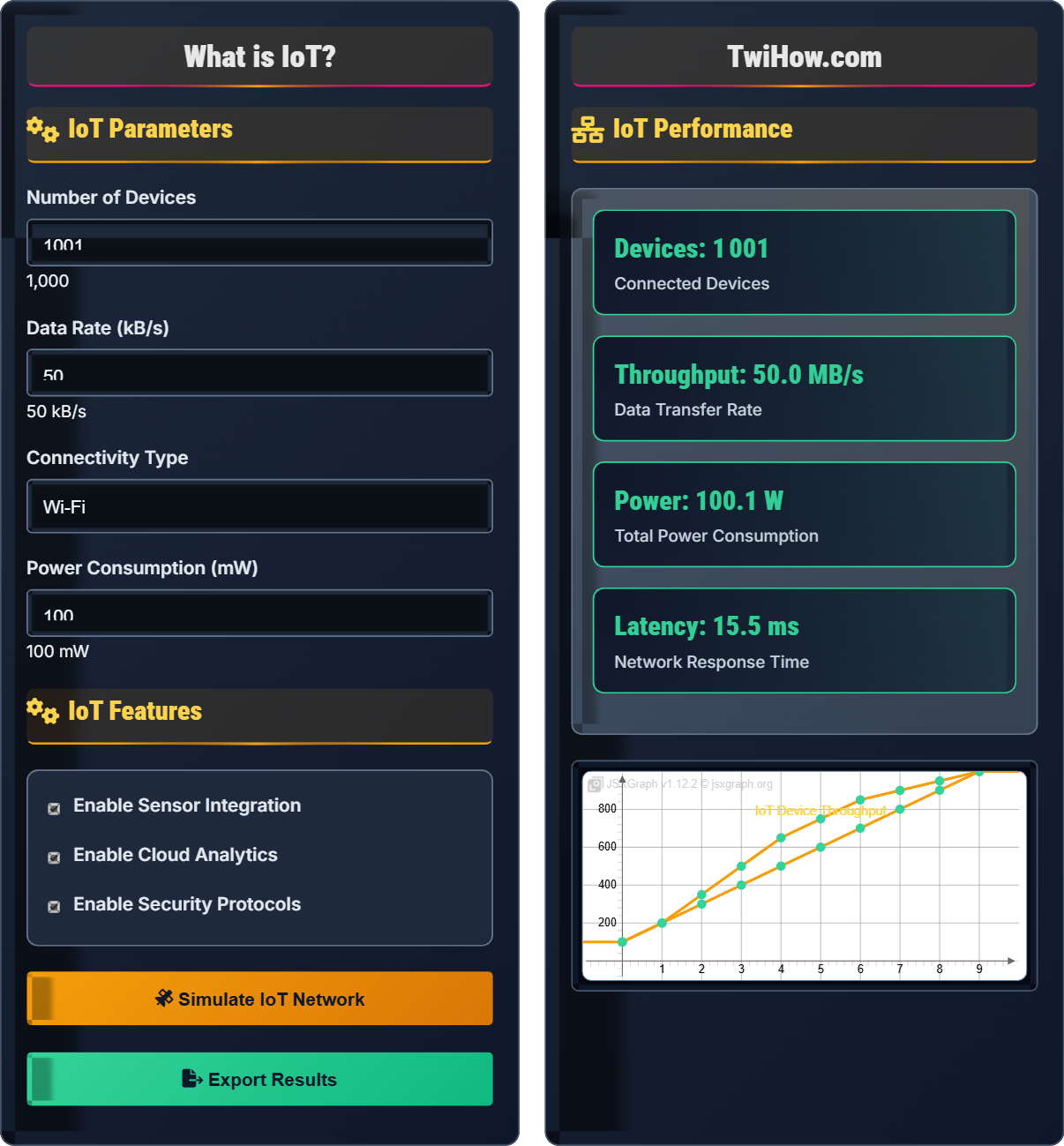
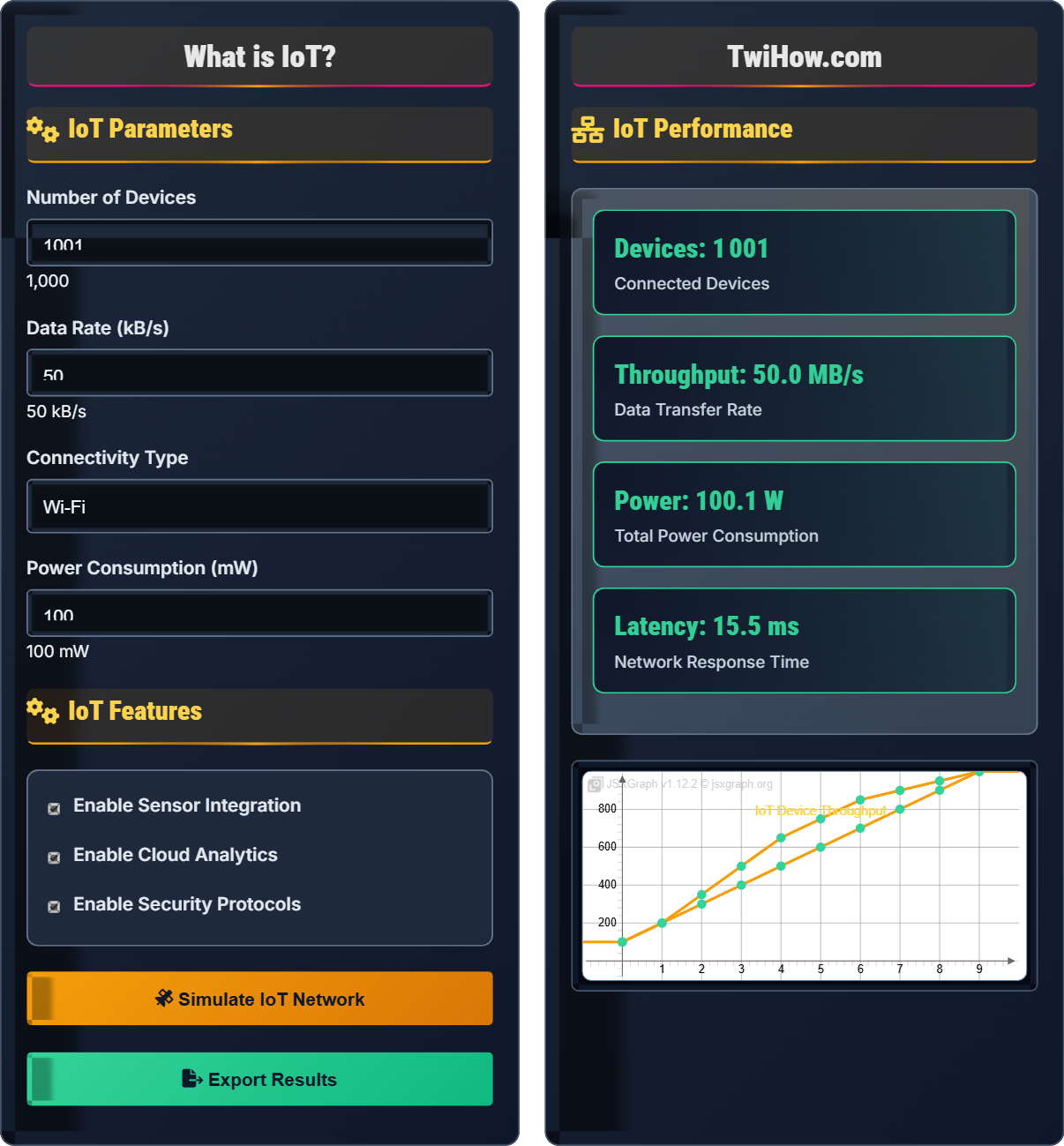
IoT Parameters
IoT Features
IoT Performance
| Device Type | Count | Data Rate | Power (mW) |
|---|---|---|---|
| Sensors | 800 | 10 kB/s | 50 |
| Actuators | 100 | 5 kB/s | 200 |
| Gateways | 50 | 100 kB/s | 500 |
| Controllers | 50 | 25 kB/s | 150 |
How IoT Technology Works
The Internet of Things (IoT) refers to a network of physical devices embedded with sensors, software, and other technologies that connect and exchange data with other devices and systems over the internet. These "smart" devices range from everyday household items to sophisticated industrial tools, all equipped with the ability to collect, process, and transmit data.
The IoT architecture consists of four main layers:
Where:
- Device Layer: Sensors and actuators collecting data
- Gateway Layer: Aggregation and preprocessing
- Cloud Layer: Storage and analytics
- Application Layer: User interface and control
IoT devices use various communication protocols:
Common protocols include:
- MQTT: Message Queuing Telemetry Transport
- CoAP: Constrained Application Protocol
- HTTP/HTTPS: Web-based communication
- LoRaWAN: Long-range, low-power networks
IoT data follows a processing pipeline:
- Data Collection: Sensors gather environmental data
- Preprocessing: Filtering and compression at edge
- Transmission: Secure data transfer to cloud
- Storage: Database systems for historical data
- Analytics: Pattern recognition and insights
- Action: Automated responses or alerts
This pipeline enables real-time monitoring and control of connected systems.
Key areas where IoT technology is transforming industries:
- Smart Homes: Automated lighting, security, climate control
- Industrial IoT: Predictive maintenance, supply chain optimization
- Healthcare: Remote patient monitoring, wearable devices
- Agriculture: Precision farming, soil monitoring
- Smart Cities: Traffic management, waste collection
- Automotive: Connected vehicles, telematics
IoT Fundamentals
Connected devices, sensors, actuators, protocols, cloud integration, edge computing.
\(\text{Data Rate} = \frac{\text{Bits Transmitted}}{\text{Time}}\)
Where data rate represents the amount of data transmitted per unit time.
- IoT devices must be low-power and cost-effective
- Security is critical at every layer
- Interoperability requires standard protocols
Applications
Smart homes, industrial automation, healthcare monitoring, precision agriculture.
- Smart manufacturing
- Connected healthcare
- Intelligent transportation
- Environmental monitoring
- Privacy and data protection concerns
- Scalability challenges
- Standardization across vendors
IoT Technology Learning Quiz
Which of the following is NOT a typical layer in the IoT architecture stack?
The traditional IoT architecture consists of four main layers: Device Layer (sensors/actuators), Gateway Layer (edge processing), Cloud Layer (storage/analysis), and Application Layer (user interfaces). While blockchain technology can be used in IoT for security and trust, it is not a standard architectural layer. The standard layers focus on the flow of data from physical devices to end-user applications.
The answer is C) Blockchain Layer.
Understanding IoT architecture is crucial because it defines how data flows through the system. The device layer collects raw data, the gateway layer preprocesses and aggregates data, the cloud layer stores and analyzes data, and the application layer presents insights to users. Each layer has specific responsibilities and technologies. While emerging technologies like blockchain can enhance IoT security, they don't constitute a fundamental architectural layer but rather an enhancement to existing layers.
IoT Architecture: Structured framework for IoT system components
Device Layer: Physical sensors and actuators
Gateway Layer: Edge processing and aggregation point
• Data flows from device to application layers
• Each layer has specific responsibilities
• Security must be implemented at every layer
• Remember the data flow direction: device → gateway → cloud → application
• Each layer can have multiple technologies
• Consider scalability at each architectural level
• Confusing IoT architecture with network protocols
• Thinking all IoT systems require cloud processing
• Ignoring edge computing capabilities
Compare MQTT and CoAP protocols for IoT communication. When should each be used, and what are their advantages and disadvantages?
MQTT (Message Queuing Telemetry Transport):
Architecture: Client-server model with message brokers
Advantages: Reliable delivery, persistent sessions, lightweight, supports Quality of Service (QoS)
Disadvantages: Requires constant TCP connection, overhead of broker infrastructure
Best for: Reliable messaging, mobile applications, scenarios requiring message persistence
CoAP (Constrained Application Protocol):
Architecture: RESTful model using UDP
Advantages: Low overhead, HTTP-like semantics, multicast support, power-efficient
Disadvantages: Less reliable than MQTT, limited transport options
Best for: Resource-constrained devices, local networks, battery-powered sensors
Both protocols are designed for IoT but address different use cases based on reliability, power, and network requirements.
The choice between MQTT and CoAP depends on the specific requirements of your IoT deployment. MQTT is like a reliable postal service that ensures your message reaches its destination, but it requires more infrastructure. CoAP is like sending a quick postcard - lighter weight but with less guarantee of delivery. The key is understanding your application's tolerance for message loss, power constraints, and network conditions. For example, a smart home might use MQTT for critical security alerts but CoAP for temperature readings that can tolerate some loss.
MQTT: Publish-subscribe messaging protocol
CoAP: RESTful protocol for constrained devices
QoS: Quality of Service levels for message delivery
• Match protocol to device capabilities
• Consider network reliability requirements
• Evaluate power consumption needs
• MQTT is better for unreliable networks
• CoAP is ideal for local IoT networks
• Both support security features
• Choosing protocol based on familiarity alone
• Ignoring device resource constraints
• Not considering network topology
A city plans to deploy 10,000 IoT sensors for traffic monitoring. Each sensor transmits 1 KB of data every 5 minutes. Calculate the total daily data volume and determine the minimum required bandwidth. If the city has a 10 Mbps connection, calculate how many concurrent sensors can be supported.
Daily Data Volume Calculation:
Per sensor per day: 1 KB × 12 transmissions/hour × 24 hours = 288 KB/day
Total for 10,000 sensors: 288 KB × 10,000 = 2,880,000 KB = 2.88 GB/day
Minimum Required Bandwidth:
Peak transmission: 10,000 sensors × 1 KB = 10,000 KB = 80,000 Kb (per 5-minute interval)
Bandwidth: 80,000 Kb ÷ 300 seconds = 266.67 Kbps average
With 10 Mbps Connection:
Each sensor requires: 1 KB ÷ 300 seconds = 0.00333 Kbps
Maximum sensors: 10,000 Kbps ÷ 0.00333 Kbps ≈ 3 million sensors
In practice, the 10 Mbps connection can easily support the 10,000 sensors with significant headroom for growth.
This problem demonstrates the importance of understanding data volume and bandwidth requirements in IoT deployments. While the total data volume might seem large, IoT data is often sparse and intermittent. The key insight is that bandwidth requirements depend on peak transmission patterns rather than total volume. Smart city deployments often aggregate data at edge gateways before transmission, significantly reducing bandwidth requirements. This is why a relatively modest 10 Mbps connection can support thousands of sensors.
Bandwidth: Maximum data transfer rate of a connection
Data Volume: Total amount of data transferredPeak Transmission: Highest data rate during operation
• IoT data is typically sparse and intermittent
• Edge aggregation reduces bandwidth needs
• Consider peak vs. average bandwidth
• Aggregate data at edge to reduce transmission
• Schedule transmissions to avoid peaks
• Compress data to save bandwidth
• Calculating bandwidth based on total volume
• Ignoring transmission timing patterns
• Not accounting for protocol overhead
Design a security framework for an IoT system containing 1,000 smart home devices. Identify the main security risks and propose mitigation strategies for each layer of the IoT architecture.
Main Security Risks:
1. Device Layer: Weak passwords, firmware vulnerabilities, physical tampering
2. Communication Layer: Eavesdropping, man-in-the-middle attacks
3. Gateway Layer: Unauthorized access, data interception
4. Cloud Layer: Data breaches, account hijacking
Mitigation Strategies:
Device Layer: Strong authentication, regular firmware updates, hardware security modules
Communication Layer: End-to-end encryption (TLS/SSL), secure protocols (MQTT with auth)
Gateway Layer: Firewall configuration, VPN tunnels, access control lists
Cloud Layer: Multi-factor authentication, encryption at rest, audit logging
Additional Measures: Network segmentation, intrusion detection systems, regular security audits, and device lifecycle management.
IoT security requires a defense-in-depth approach because each layer has unique vulnerabilities. At the device level, weak default passwords and unpatched firmware create entry points. Communication channels must be encrypted to prevent eavesdropping. Gateways need to be secured as they aggregate data from multiple devices. Cloud platforms require robust access controls since they store sensitive data. The key principle is that security must be implemented at every layer - a single weak link can compromise the entire system.
Defense-in-Depth: Multiple layers of security controls
TLS/SSL: Transport Layer Security/Secure Sockets Layer
MFA: Multi-Factor Authentication
• Security must be implemented at every layer
• Regular updates are critical for IoT devices
• Network segmentation isolates threats
• Change default passwords immediately
• Use certificate-based authentication
• Monitor device behavior for anomalies
• Treating IoT security as an afterthought
• Using weak or default credentials
• Neglecting firmware updates
Which of the following represents a fundamental challenge in IoT deployments?
One of the biggest challenges in IoT is the lack of standardization and interoperability between devices from different manufacturers. The absence of universal standards means that IoT devices often use proprietary protocols and communication methods, making it difficult to integrate devices from different vendors into a unified system. This fragmentation creates silos and limits the full potential of IoT ecosystems.
The answer is C) Standardization and interoperability.
The IoT industry suffers from a "Tower of Babel" problem where devices speak different languages. While technically feasible to connect thousands of devices, the reality is that they often can't communicate with each other effectively. This is why smart home ecosystems from different vendors don't always work together seamlessly. Standards bodies are working on solutions (like Matter protocol), but adoption takes time. This is why successful IoT deployments often start with devices from a single vendor or focus on specific use cases where interoperability is less critical.
Interoperability: Ability of different systems to work together
Proprietary Protocols: Vendor-specific communication methods
IoT Silos: Isolated IoT ecosystems that don't communicate
• Standardization is still evolving
• Vendor lock-in is a real concern
• Plan for future integration needs
• Look for open standards compliance
• Consider APIs and integration capabilities
• Plan for mixed-vendor environments
• Assuming all IoT devices can interoperate
• Not planning for multi-vendor integration
• Ignoring future expansion needs
FAQ
Q: How do IoT devices communicate with each other?
A: IoT devices communicate through various methods:
1. Direct Communication: Devices can communicate directly using protocols like Bluetooth, Zigbee, or Z-Wave.
2. Cloud-Mediated: Devices send data to cloud servers, which then relay information to other devices.
3. Gateway Communication: Local gateways collect data from multiple devices and coordinate communication.
4. Mesh Networks: Devices relay messages to each other, extending network coverage.
The choice depends on factors like range, power consumption, data rate, and security requirements. Most IoT systems use a combination of these approaches.
Q: What are the main business benefits of IoT?
A: IoT offers several key business benefits:
Operational Efficiency: Real-time monitoring and predictive maintenance reduce downtime and optimize resource utilization.
Cost Reduction: Automated processes and optimized operations decrease labor and operational costs.
New Revenue Streams: Data-driven services and subscription models create new income sources.
Enhanced Customer Experience: Personalized services and real-time support improve customer satisfaction.
Competitive Advantage: Early IoT adopters gain market differentiation and operational insights.
However, businesses must also consider implementation costs, security requirements, and staff training investments.