What is Cryptocurrency and is it Safe?
Complete crypto guide • Safety analysis • Step-by-step explanations
Cryptocurrency Fundamentals:
Analyze Crypto SafetyCryptocurrency is a digital or virtual currency that uses cryptography for security. A cryptocurrency is difficult to counterfeit because of this security feature. A defining characteristic of a cryptocurrency, and arguably its biggest allure, is its organic nature; it is not issued by any central authority, rendering it theoretically immune to government interference or manipulation.
Cryptocurrencies operate on decentralized networks based on blockchain technology—a distributed ledger enforced by a disparate network of computers. This technology allows for secure, transparent, and tamper-resistant transactions.
Key characteristics:
- Decentralization: No central authority controls the network
- Transparency: All transactions are publicly recorded
- Immutability: Once recorded, transactions cannot be altered
- Global Accessibility: Available 24/7 worldwide
Regarding safety, cryptocurrencies have both inherent security features and significant risks that investors and users should understand before participating in the crypto ecosystem.
Cryptography
Cryptographic techniques secure transactions and control creation of new units. Mathematical algorithms make counterfeiting virtually impossible.
Blockchain
Distributed ledger technology that records all transactions across a network of computers, ensuring transparency and immutability.
Decentralization
No central authority controls the network, making it resistant to censorship and single points of failure.
Peer-to-Peer
Direct transactions between parties without intermediaries like banks, reducing costs and increasing speed.
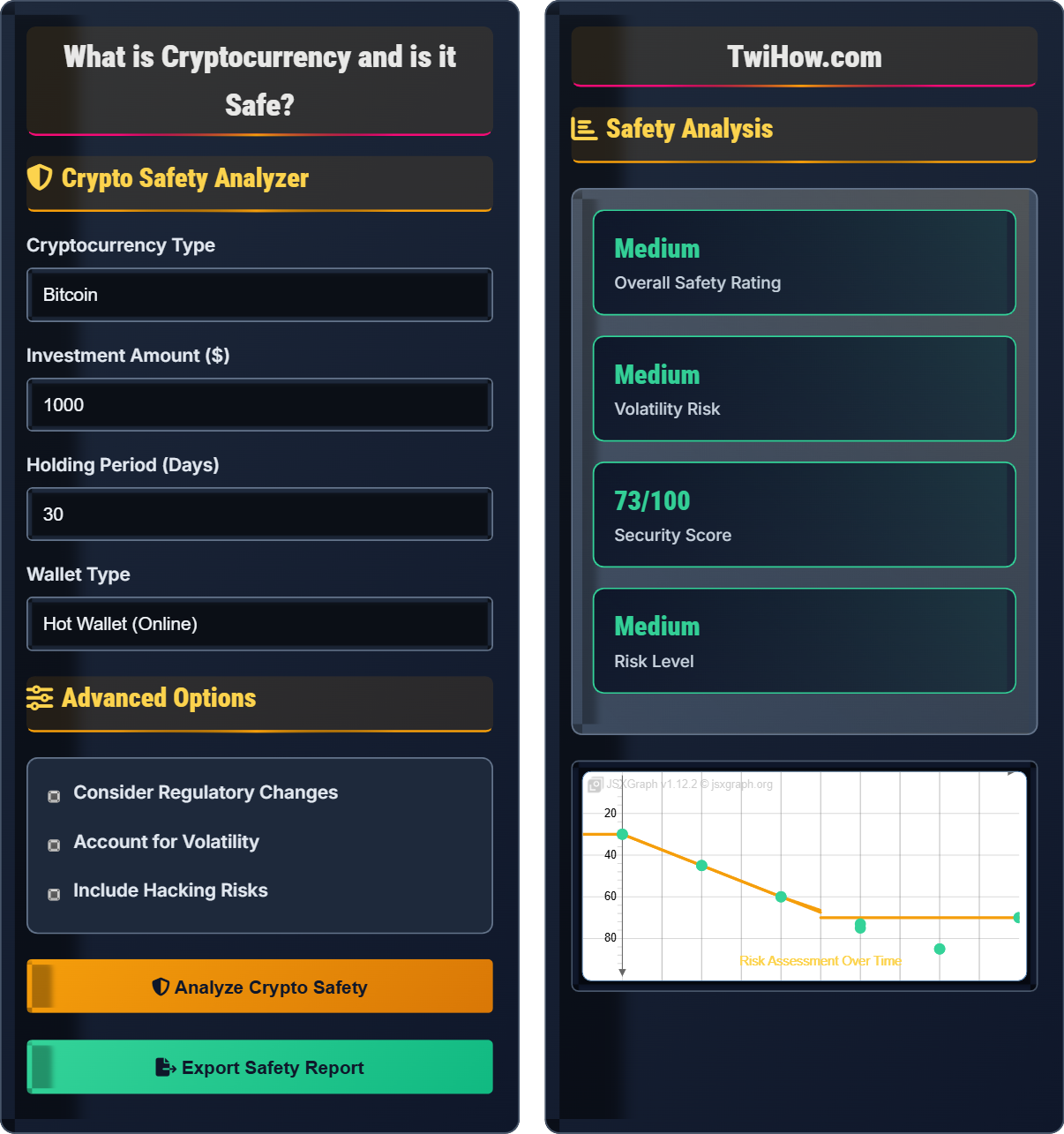
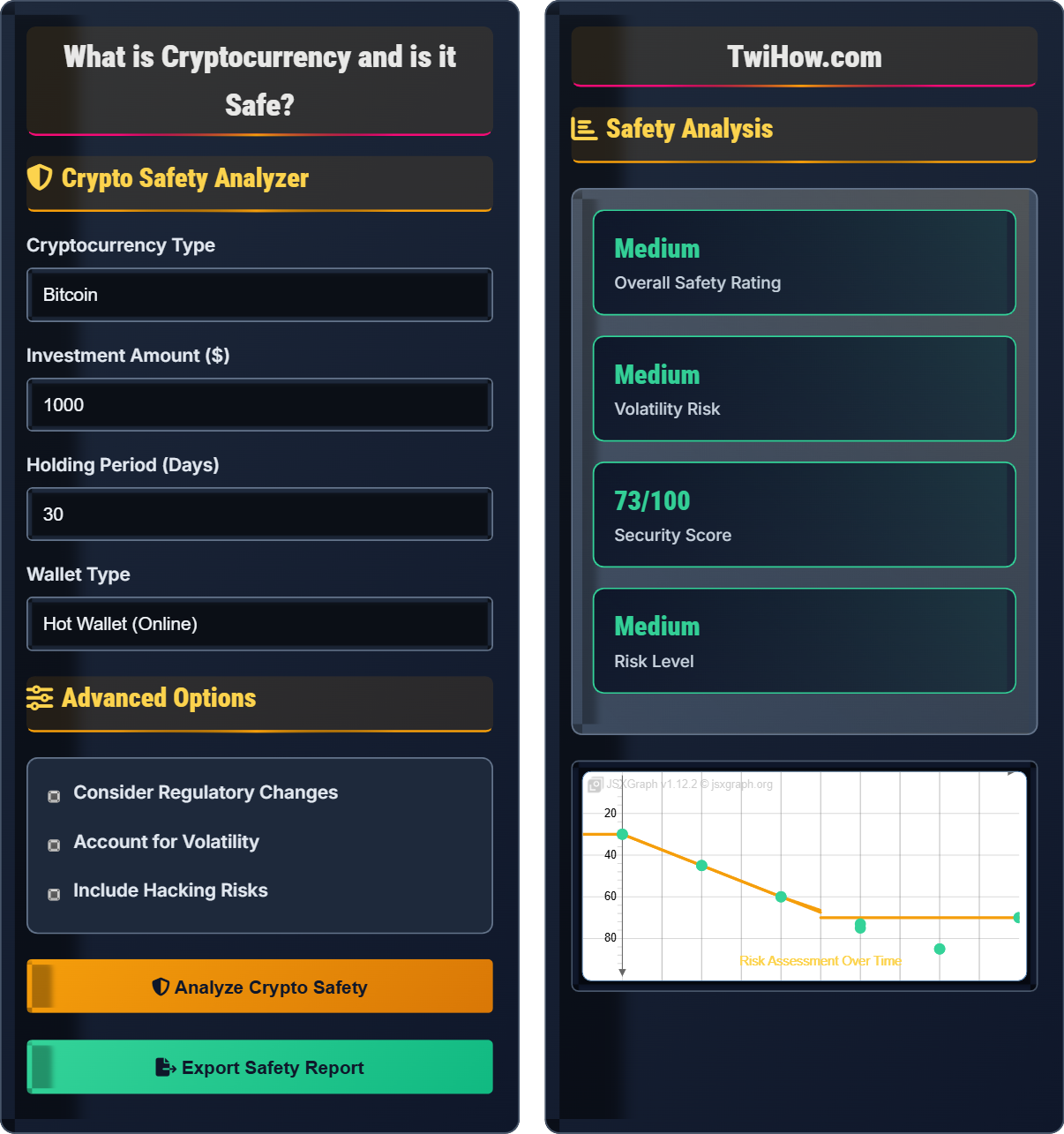
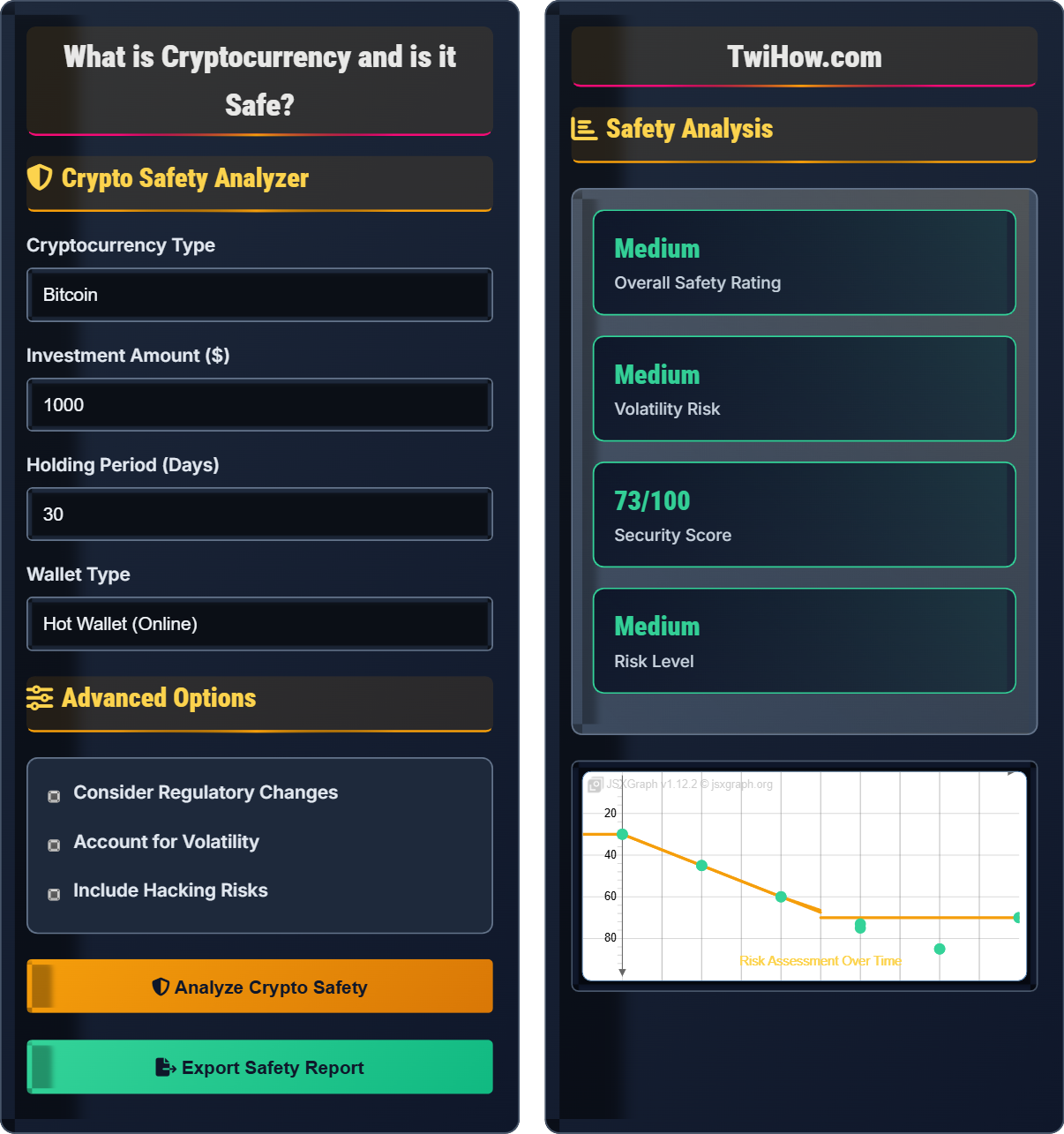
Crypto Safety Analyzer
Advanced Options
Safety Analysis
| Risk Factor | Severity | Mitigation | Status |
|---|---|---|---|
| Market Volatility | High | Diversification, Dollar-cost averaging | |
| Hacking Threats | Medium | Secure wallets, 2FA | |
| Regulatory Changes | Medium | Stay informed, Compliance | |
| Technology Obsolescence | Low | Follow development, Upgrade |
Wallet Security
Transaction Safety
Blockchain Technology Explained
Blockchain is a distributed ledger technology that records transactions across many computers in such a way that the registered transactions cannot be altered retroactively.
Mining Process
Risk Assessment Matrix
The overall safety of cryptocurrency depends on multiple factors including the specific cryptocurrency, storage method, and market conditions.
Cryptocurrency Explained
Cryptocurrency is a digital or virtual currency that uses cryptography for security. A cryptocurrency is difficult to counterfeit because of this security feature. A defining characteristic of a cryptocurrency, and arguably its biggest allure, is its organic nature; it is not issued by any central authority, rendering it theoretically immune to government interference or manipulation.
Cryptocurrencies operate on decentralized networks based on blockchain technology—a distributed ledger enforced by a disparate network of computers. This technology allows for secure, transparent, and tamper-resistant transactions.
Cryptographic techniques secure transactions and control creation of new units. Key concepts include:
- Hash Functions: One-way functions that convert data into fixed-length strings
- Digital Signatures: Verify ownership and authenticity of transactions
- Public/Private Keys: Asymmetric encryption for secure transactions
- Proof of Work: Consensus mechanism requiring computational effort
Main categories of cryptocurrencies:
- Bitcoin: First cryptocurrency, primarily store of value
- Ethereum: Platform for smart contracts and dApps
- Stablecoins: Pegged to stable assets like USD
- Altcoins: Alternative cryptocurrencies with various uses
- Utility Tokens: Provide access to specific platforms
- Security Tokens: Represent ownership in assets
Advantages:
- Decentralization and no central authority
- Global accessibility and 24/7 operation
- Potential for high returns
- Reduced transaction costs
- Enhanced privacy features
Disadvantages:
- Extreme price volatility
- Regulatory uncertainty
- Security risks and scams
- Environmental concerns
- Technical complexity
Cryptocurrency Fundamentals
Blockchain, cryptography, decentralization, mining, consensus mechanisms, digital wallets.
H(m) = SHA-256(m)
Where H = hash function, m = message/data, SHA-256 = Secure Hash Algorithm 256-bit.
- Never share private keys
- Use secure wallets for storage
- Verify addresses before transactions
Safety Considerations
Private keys, public addresses, 2FA, cold storage, hardware wallets, phishing protection.
- Use hardware wallets for large amounts
- Enable two-factor authentication
- Backup seed phrases securely
- Verify exchange legitimacy
- Only invest what you can afford to lose
- Stay informed about regulations
- Be aware of market volatility
Crypto Learning Quiz
What makes blockchain technology secure against tampering?
Blockchain security relies on cryptographic hashing, where each block contains a hash of the previous block. This creates an immutable chain - changing any data in a block would require recalculating all subsequent hashes, which is computationally infeasible due to the distributed nature of the network and the proof-of-work consensus mechanism.
The answer is B) Cryptographic hashing.
Each block in a blockchain contains a unique cryptographic fingerprint (hash) of the previous block, along with its own data. This creates a chain of blocks that are mathematically linked. To alter a transaction in an earlier block, a malicious actor would need to recalculate the hashes for all subsequent blocks, which requires controlling more than 50% of the network's computing power. This is what makes blockchain tamper-resistant.
Hash Function: Mathematical function that converts data into fixed-length string
Immutable: Cannot be changed or altered
Proof of Work: Consensus mechanism requiring computational effort
• Blocks are cryptographically linked
• Changing history requires massive computation
• Network validates all transactions
• Think of blockchain as a linked chain
• Breaking a link affects the whole chain
• Confusing blockchain with Bitcoin
• Thinking blockchain can be easily modified
• Assuming blockchain is always secure
Explain the role of private keys in cryptocurrency security and why they must never be shared. What happens if someone gains access to your private key?
Private Keys: Private keys are secret codes that prove ownership of cryptocurrency. They are used to sign transactions, authorizing transfers of coins from your wallet.
Security Role: Private keys are mathematically linked to public addresses but cannot be derived from them. They provide cryptographic proof of ownership without revealing the private key itself.
Why Not to Share: Anyone with access to your private key can control your cryptocurrency holdings. Sharing it is equivalent to giving someone complete access to your digital assets.
Compromise Consequences: If someone gains access to your private key, they can transfer all your cryptocurrency to their own wallet, and you have no way to recover it since there's no central authority to appeal to.
Private keys function like passwords to bank accounts, but with a critical difference: there's no way to reset or recover them if lost, and no institution to reverse unauthorized transactions. The mathematical relationship between private keys and public addresses uses elliptic curve cryptography, making it practically impossible to derive a private key from a public address, but trivial to use a private key to authorize transactions.
Private Key: Secret code proving ownership of crypto assets
Public Address: Shareable identifier for receiving crypto
Digital Signature: Cryptographic proof of transaction authorization
• Never share private keys with anyone
• Store them offline in secure locations
• Use hardware wallets for large amounts
• Write down seed phrases on paper
• Store in fireproof containers
• Never save on cloud services
• Storing private keys in plain text
• Sharing them via email/social media
• Using online generators for key creation
Sarah invests $5,000 in Bitcoin. The price fluctuates dramatically: +15% on Monday, -8% on Tuesday, +12% on Wednesday, -5% on Thursday, and +3% on Friday. Calculate her final portfolio value and determine the overall percentage change. What does this demonstrate about cryptocurrency volatility?
Day-by-day calculation:
Starting: $5,000
Monday: $5,000 × 1.15 = $5,750
Tuesday: $5,750 × 0.92 = $5,290
Wednesday: $5,290 × 1.12 = $5,925
Thursday: $5,925 × 0.95 = $5,629
Friday: $5,629 × 1.03 = $5,798
Overall Change: (($5,798 - $5,000) / $5,000) × 100 = 15.96%
This example demonstrates extreme volatility in cryptocurrency markets, where substantial daily price swings can occur. Even though the week ended positively, Sarah experienced significant intra-week fluctuations, highlighting the risk associated with crypto investments.
This example illustrates the dramatic price volatility characteristic of cryptocurrency markets. Unlike traditional assets, crypto prices can swing 10% or more in a single day. This volatility can create opportunities for significant gains but also poses substantial risk of losses. Investors should be prepared for these fluctuations and only invest money they can afford to lose.
Volatility: Degree of variation in trading prices over time
Percentage Change: Relative change in value expressed as percentageIntra-week Fluctuation: Price changes within a single week
• Crypto prices can swing dramatically daily
• Past performance doesn't predict future results
• Only invest what you can afford to lose
• Use dollar-cost averaging to reduce timing risk
• Set stop-loss orders to limit losses
• Diversify across different assets
• Investing more than you can afford to lose
• Making emotional decisions during volatility
• Not having a clear investment strategy
An investor wants to securely store $100,000 worth of cryptocurrency. Compare the security trade-offs between hot wallets (online), cold wallets (hardware), and paper wallets. Recommend the best option and explain your reasoning considering the investment amount.
Hot Wallets: Convenient for frequent trading but vulnerable to hacking. Connected to internet, accessible via apps/computers.
Cold Wallets: Hardware devices completely offline, most secure for large amounts. Require physical access to transact.
Paper Wallets: Physical printouts of private keys, immune to digital attacks but susceptible to physical damage/loss.
Recommendation: For $100,000, a hardware wallet (cold storage) is optimal. It offers the highest security while maintaining usability. Hot wallets are too risky for this amount, and paper wallets are impractical for regular access.
Security needs scale with the value of holdings. For small amounts, convenience might outweigh security, but as values increase, security becomes paramount. Hardware wallets strike the best balance between security and usability for substantial holdings. They're protected from online threats while still allowing controlled access when needed.
Hot Wallet: Internet-connected wallet for frequent access
Cold Wallet: Offline storage device for maximum security
Trade-off: Balance between security and convenience
• Scale security with investment value
• Never keep large amounts in hot wallets
• Have backup and recovery plans
• Use multiple hardware wallets for diversification
• Keep small amounts in hot wallets for trading
• Test recovery process before storing large amounts
• Storing large amounts in exchange wallets
• Not backing up seed phrases properly
• Using only one security method
Which of the following is the GREATEST regulatory risk facing cryptocurrency investors?
A complete ban in major economies would have the most severe impact on cryptocurrency values and viability. While taxation, reporting, and licensing create operational challenges, a ban would eliminate the legal framework for cryptocurrency use and trading in those jurisdictions, potentially causing massive sell-offs and devaluation. The global nature of crypto means that major economy bans could severely impact the entire ecosystem.
The answer is B) Complete ban in major economies.
Regulatory risk is one of the most significant factors affecting cryptocurrency prices. Government policies can instantly change the legal landscape for crypto. While some regulations provide clarity and legitimacy, outright bans eliminate the possibility of legal participation in the market, which could cause widespread panic selling and devaluation. Investors must stay informed about regulatory developments in major markets.
Regulatory Risk: Potential negative impact of government regulations
Legal Framework: Laws governing cryptocurrency use and trading
Market Legitimacy: Acceptance and regulation by authorities
• Monitor regulatory developments regularly
• Understand jurisdiction-specific laws
• Diversify across regulatory environments
• Follow official government announcements
• Consult with legal experts
• Stay updated on regulatory proposals
• Ignoring regulatory changes
• Assuming crypto is unregulated globally
• Not understanding local laws
FAQ
Q: Is cryptocurrency safer than traditional banking?
A: The safety comparison depends on different aspects:
Traditional Banking: FDIC insurance protects deposits up to $250,000; regulated institutions; consumer protections; government oversight. However, banks can freeze accounts, charge fees, and restrict access.
Cryptocurrency: No deposit insurance; self-custody responsibility; irreversible transactions. However, no account freezing, global access, and protection against inflation.
Conclusion: Traditional banking offers more institutional protections, while crypto offers more personal control but requires more personal security responsibility. The "safer" option depends on your risk tolerance and security practices.
Q: How do I safely store my cryptocurrency?
A: The safest storage methods depend on your needs:
For Large Holdings: Hardware wallets (Ledger, Trezor) offer the best security by keeping private keys offline. Store in a secure location and create multiple backups of your recovery phrase.
For Active Trading: Use reputable exchanges with strong security features, but keep only what you're actively trading. Never leave large amounts on exchanges.
For Maximum Security: Paper wallets (private keys printed on paper) are immune to digital attacks but vulnerable to physical damage and theft.
Best Practices: Enable 2FA, verify addresses before sending, keep software updated, and never share private keys or recovery phrases.
Q: What causes cryptocurrency prices to be so volatile?
A: Several factors contribute to crypto volatility:
Market Maturity: Cryptocurrency markets are relatively new and less liquid than traditional markets, making them more susceptible to large price swings from smaller trades.
Regulatory News: Announcements about regulation can cause dramatic shifts as markets price in potential impacts.
Speculative Nature: Many investors treat crypto as speculative assets rather than stores of value, leading to emotional trading decisions.
Media Influence: Social media and news can rapidly influence market sentiment, especially with influential figures making public statements.
Technological Developments: Updates to protocols, new use cases, or security vulnerabilities can significantly impact prices.
As the market matures and adoption increases, volatility is expected to decrease somewhat, though crypto will likely remain more volatile than traditional assets.